Americans' abysmal cyber-hygiene is bad news for individuals at risk of attack, but the stakes are far higher for the companies that employ them. Especially when employees work from home or bring tech with them on work trips, they're likely to expose the company's entire infrastructure to a potential risk.
What's the answer? Business owners need to conduct regular IT audits to make sure that their systems are uncompromised and their employees are up-to-date on their cybersecurity know-how. These audits also provide a way to be sure costs, speeds, and protocols are on point. If it's your first time tackling an IT audit, our checklist will guide you through the basics.
Table of contents:
What is an IT audit?
An IT audit is an evaluation of an organization's information technology infrastructure (including devices), policies, and procedures. It's designed to ensure that IT systems are functioning properly and securely and that employees are abiding by security standards by using them safely and correctly.
Depending on how large your organization is, you can either run a single comprehensive IT audit or audit different areas of your infrastructure individually. And depending on what your IT processes look like, there are a few different types of IT audits you can consider to shore up security. Here are some examples:
Cybersecurity audits: These audits look for potential weaknesses hackers or other bad actors can exploit to access protected data.
Enterprise-level IT structure audits: Because IT processes are more effective at scale when they have a defined structure, it's worthwhile to analyze how they've been organized.
Existing systems and applications audits: Businesses can audit the security measures for all existing systems and applications.
Developing systems and applications audits: As businesses create new IT systems to meet their changing needs, they should be audited to ensure they're aligned with existing security standards.
Physical IT facility audits: Businesses can audit the conditions and security measures in place at the physical locations related to their essential IT infrastructure.
Third-party audits: It can be worthwhile to assess how well third-party applications are performing and how they affect the business's broader IT infrastructure.
Server audits: These audits assess the business's overall network security performance and whether it meets compliance standards.
Across the board, the goal is to assess the risks associated with your IT systems and to find ways to mitigate those risks, either by solving existing problems, correcting employee behavior, or implementing new systems.
Why you should perform IT audits regularly
In short: because everything your business does depends on a functioning IT ecosystem. Technology, like Bob Dylan once said, is a-changin', and so are cyber threats. Regular IT audits ensure your IT operations are keeping up with evolving standards in software and hardware while staying vigilant in the face of smarter and smarter cyber attackers.
More specifically, IT audits help businesses:
Uncover previously unseen security risks within existing processes
Ensure all their assets are secure and have been properly updated
Identify potential vulnerabilities before they can be exploited
Maintain privacy and security compliance measures like 2FA and secure emailing
Find inefficiencies in IT processes and address them before they become obstacles
Adapt to evolving security needs and standards like growing AI risks
Gain actionable business insights from traditionally siloed IT processes
Promote trust for employees, customers, and vendors
Save money in the long term by keeping IT operations running efficiently and preventing costly outages
IT audit checklist
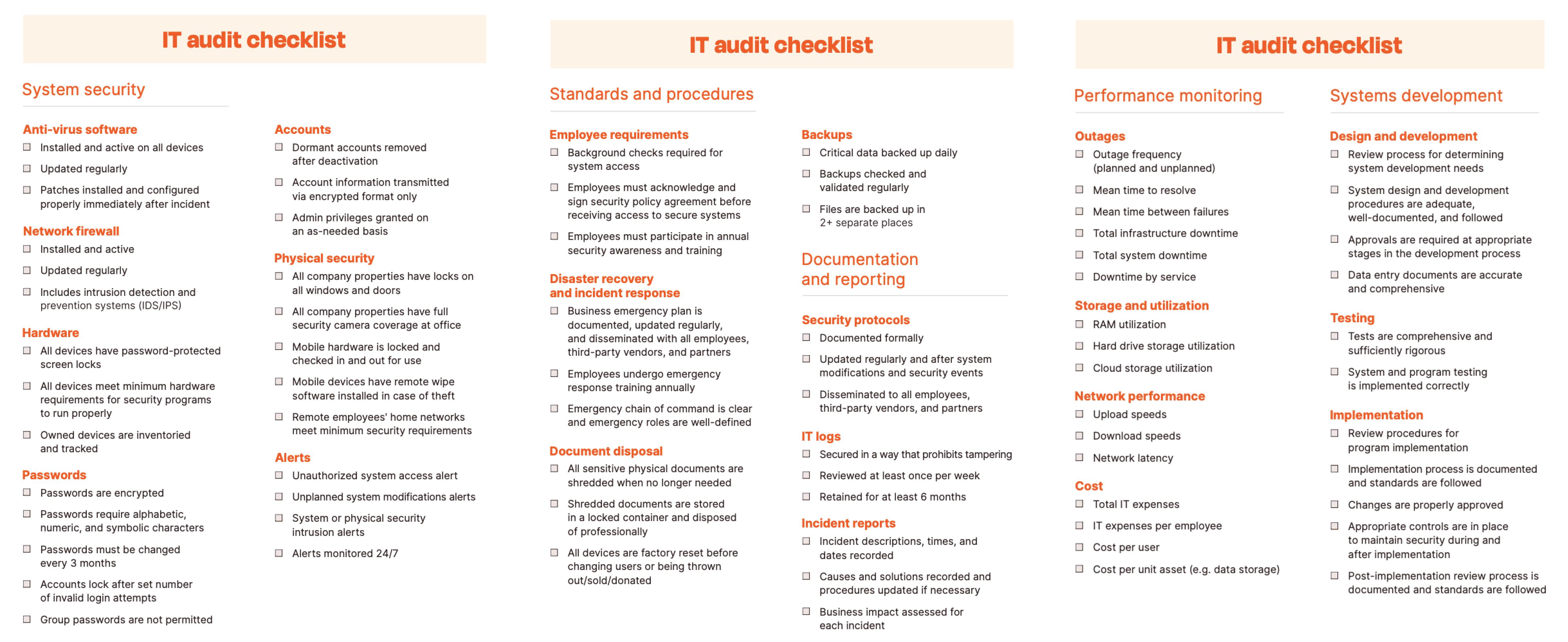
If you're already ready to execute your next IT audit—congrats, no need to read the rest of this post.
You'll also do well to keep these complex processes and detailed procedures organized with a dedicated doc. The IT checklist above divides common audit tasks into five typical IT buckets we'll explore in the next section in more detail: system security, standards and procedures, documentation and reporting, performance monitoring, and systems development.
Keep in mind that a checklist, while essential, isn't sufficient internal documentation for an audit. The point of running this evaluation is to get a detailed understanding of your infrastructure's weaknesses and tailored, actionable steps you can take to remedy them. In order to do that, you'll need a more sophisticated system than paper and a clipboard.
5 key areas of an IT audit
Usually, IT audits are conducted by an organization's IT manager or cybersecurity director (in smaller organizations, those roles may be occupied by the business owner or head of operations). There are five key areas of an IT audit that more or less correspond with an IT manager's key responsibilities:
System security: From checking antivirus software to ensuring password management best practices to setting up alert monitoring, these essentials keep systems secure.
Standards and procedures: This will help you manage ongoing protocols for essential practices like disaster recovery, document disposal, and securing backups.
Documentation and reporting: This helps you keep your processes for security, logs, and incident reporting transparent year-round.
Performance monitoring: Steps in this section help your teams keep sound documentation of things like outages, network performance, and IT costs.
Systems development: These items ensure your audit accounts for system development, testing, and implementation.
Within each of these areas, the auditor will run through a checklist of items to evaluate. Our audit checklist covers all of the steps of a basic IT audit, but depending on your infrastructure needs, you may find that you need to add areas or that some of those listed aren't necessary for your company.

IT audit process: 5 steps
Though the IT audit itself usually happens over the course of a few days, the process really begins long before that, when you take a look at your calendar and start laying out plans to schedule an audit in the future.
Step 1: Plan the audit
The first decision you'll need to make is whether to conduct an internal audit or hire an outside auditor to come in and offer a third-party perspective on your IT systems. External audits are more common in large corporations or companies that handle sensitive data. For the majority of companies, an internal audit is more than adequate and will be a lot less expensive to plan. If you want a little extra peace of mind, you might establish a yearly internal audit and hire an outside auditor once every few years.
When planning your audit, you'll need to decide:
Who your auditor will be (whether that means choosing an outside auditor or identifying an employee to be responsible for the audit)
When your audit will take place
What processes you need to establish to prepare your employees for the audit
An auditor will likely need to speak with different employees and team managers to learn about your company's IT workflows, so it's important to make sure you're not booking your audit for a time when your employees are swamped with other work.
Step 2: Prepare for the audit
Once you have a general time frame hammered out, you'll need to work with your audit team to prepare for the audit itself. A shortlist of things you'll need to figure out in this stage includes:
Your audit objectives
The scope of the audit (what areas are being evaluated, and at what level of detail the auditor will perform their evaluation)
How the audit will be documented
A detailed audit schedule (which departments will be evaluated on different days, and how much time departments should plan to dedicate to the audit)
And if you really want to make sure you've dotted your I's and crossed your T's, you can use our aforementioned checklist to keep your IT audit processes organized while you plan them out.
Step 3: Conduct the audit
Yup, conducting the audit is only step three in the five-step audit process. This step is pretty self-explanatory—if you did step two correctly, then step three will just be to execute the plan you created.
Keep in mind that even the best laid plans of mice and men (or I guess in this case, mice and keyboards) do often go awry, so this step may also include finding a way around any last-minute obstacles. Make sure you build in plenty of time so that you're not in a rush—if you wind up missing things in the audit, that defeats its whole purpose.
Step 4: Report your findings
After your audit is finished, you should have a hefty file of documentation to show for it with your auditor's notes, findings, and suggestions. The next step is to synthesize this information into an official audit report. This is the document you'll put on file for future reference and to help plan next year's audit.
Then, you'll want to create individual reports for the heads of each audited department. Summarize what was evaluated, run down the items that don't need changes, and highlight anything the department is doing really well. Then, give a rundown of the vulnerabilities the auditor identified, and separate them according to their cause:
Risks caused by poor adherence to established procedures will require corrective action.
Risks caused by vulnerabilities that had gone unnoticed prior to the audit will require new solutions.
Risks that are inherent to the department's work likely can't be eliminated completely, but the auditor may identify ways to mitigate them.
Along with each item, explain what the next steps will be in order to address the identified risks. In situations where risks were caused by willful carelessness, you may also want to loop in your HR department for guidance on how to handle the issue.
Step 5: Follow up
Let's be realistic: many (if not most) infrastructure vulnerabilities are caused at least in part by human error. Human error is just as likely to interfere with the solutions your team implements to correct the risks identified by the audit.
After you deliver your report findings, put a date on the calendar to follow up with each team and ensure that corrections were implemented successfully. It's wise to schedule a few follow-ups throughout the year to check in with each team and make sure that everything continues to run smoothly until your next audit.
What about IT audit courses and certifications?
If you decide to handle your IT audits internally, it's a good idea to designate an auditor ahead of time and have them take relevant IT auditing courses to gain IT audit certification. Here are a few popular certifications to consider:
Certified Information Systems Auditor (CISA): This is probably the best-known IT audit certification, offered by the Information Systems Audit and Control Association (ISACA).
Certification in Risk and Information Systems Control (CRISC): Also offered by ISACA, this certification is good for those who want to focus on risk management.
Certified Information Systems Security Professional (CISSP): Offered by the International Information System Security Certification Consortium (ISC2), this certification is globally recognized for IT audits.
GIAC Systems and Network Auditor (GSNA): Another globally known certification, offered by Global Information Assurance Certification (GIAC), this helps IT professionals hone their technical auditing skills.
Certified Internal Auditor (CIA): The Institute of Internal Auditors (IIA) offers this versatile certification that's technically designed for broader internal auditing than just IT.
IT audit certifications aren't necessary, but they have a few pretty convincing advantages, like validating the security of your IT infrastructure, ensuring your teams are abiding by auditing fundamentals, and improving overall audit effectiveness. Let's just say it sounds a lot better when you can say your tech is backed by regular certified audits than it is to say your tech has occasional audits by an unnamed IT guy.
Keep in mind that certification takes time, so be prepared for your future auditor to set aside time to study up for their exam and pass it. Plus, there are other possible requirements, like mandatory work experience, application processing times, and the potential need to retake the exam.
The auditor will also need to maintain their certification, so once they're certified, it can be helpful to work checkpoints into their ongoing responsibilities to ensure they're keeping up with requirements.
Automating your IT audits
As your company begins to move forward with its new solutions in place, set up dashboards for automatic KPI tracking and reporting, so you can measure the impact of each change. When you check in with your team in the months following your audit, pull these reports so that you can assess performance and troubleshoot anything that's not working the way you expected it to.
You can also set up automations to do these "check-ins" for you by running regular vulnerability scans and monitoring system performance. Instead of filling your calendar with individual check-in meetings, you can let your tech handle the heavy lifting and only get involved when you get an alert.
As you get more comfortable with the process and begin following up, here's a guide for how to automate your IT management.
Related reading:
This article was originally published in August 2022 by Amanda Pell. The most recent update was in August 2024.