The secure way to scale AI
Don’t compromise. Zapier is the only AI orchestration platform that combines the oversight IT demands with the speed your business teams need.
Zapier is trusted by companies where security comes first
- Identity and Access Management
- Financial Services
- Biotech SaaS
- Audit Management Software
- Cloud Storage
- Industrial Technology
Full visibility
Security built into every workflow
Your teams are connecting AI tools to your business systems. Each one works great alone. The question is whether they work together — safely, visibly, without collisions.
Enterprise-grade security
Maintain SOC 2 Type II, SOC 3, GDPR, and CCPA compliance
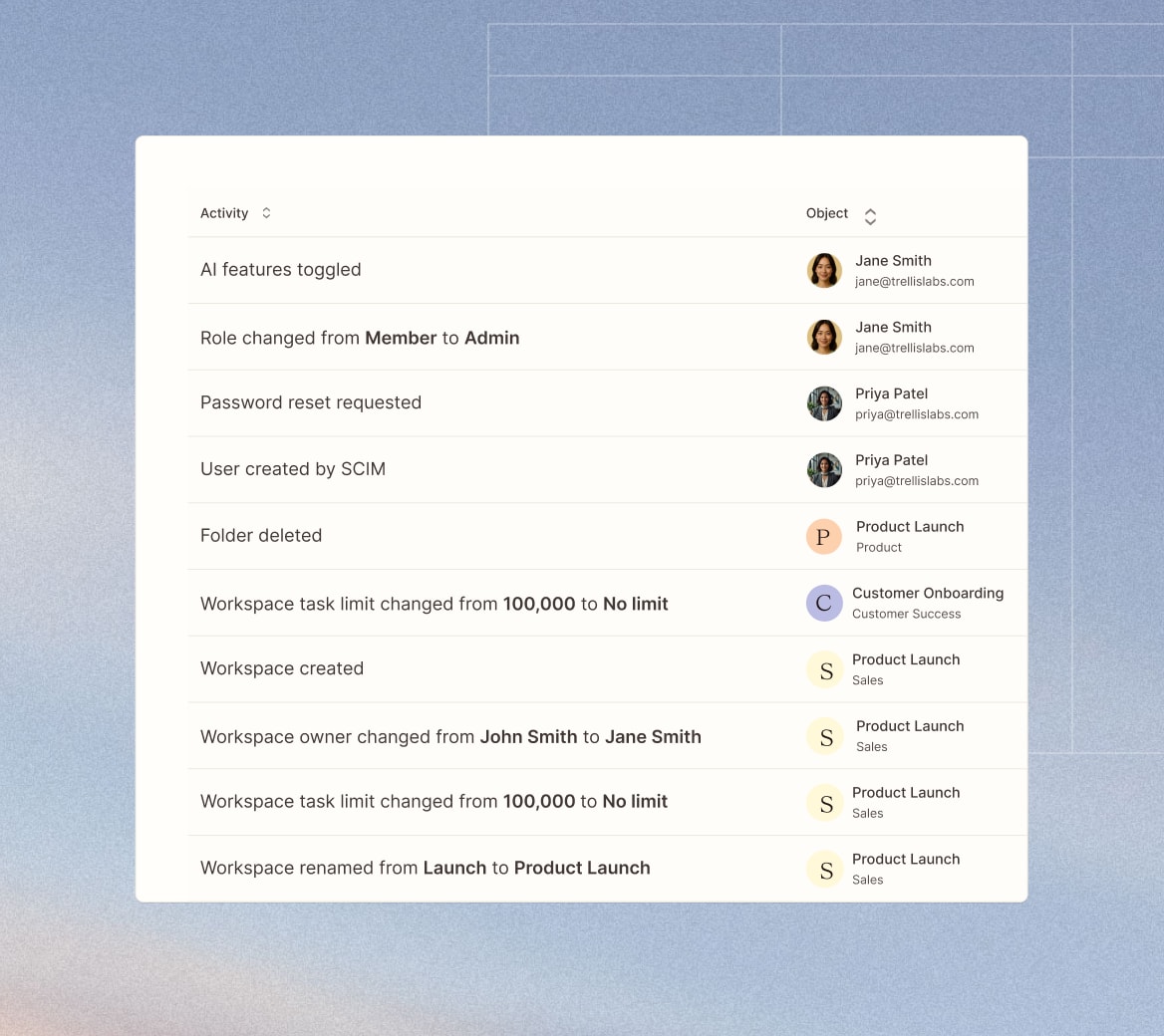
- Every execution logged, every connection tracked
- Query: "All workflows touching HubSpot in 7 days"
- User attribution — who, when, from where
- Immutable — cannot be retroactively modified
Centralized access management
Granular permissions
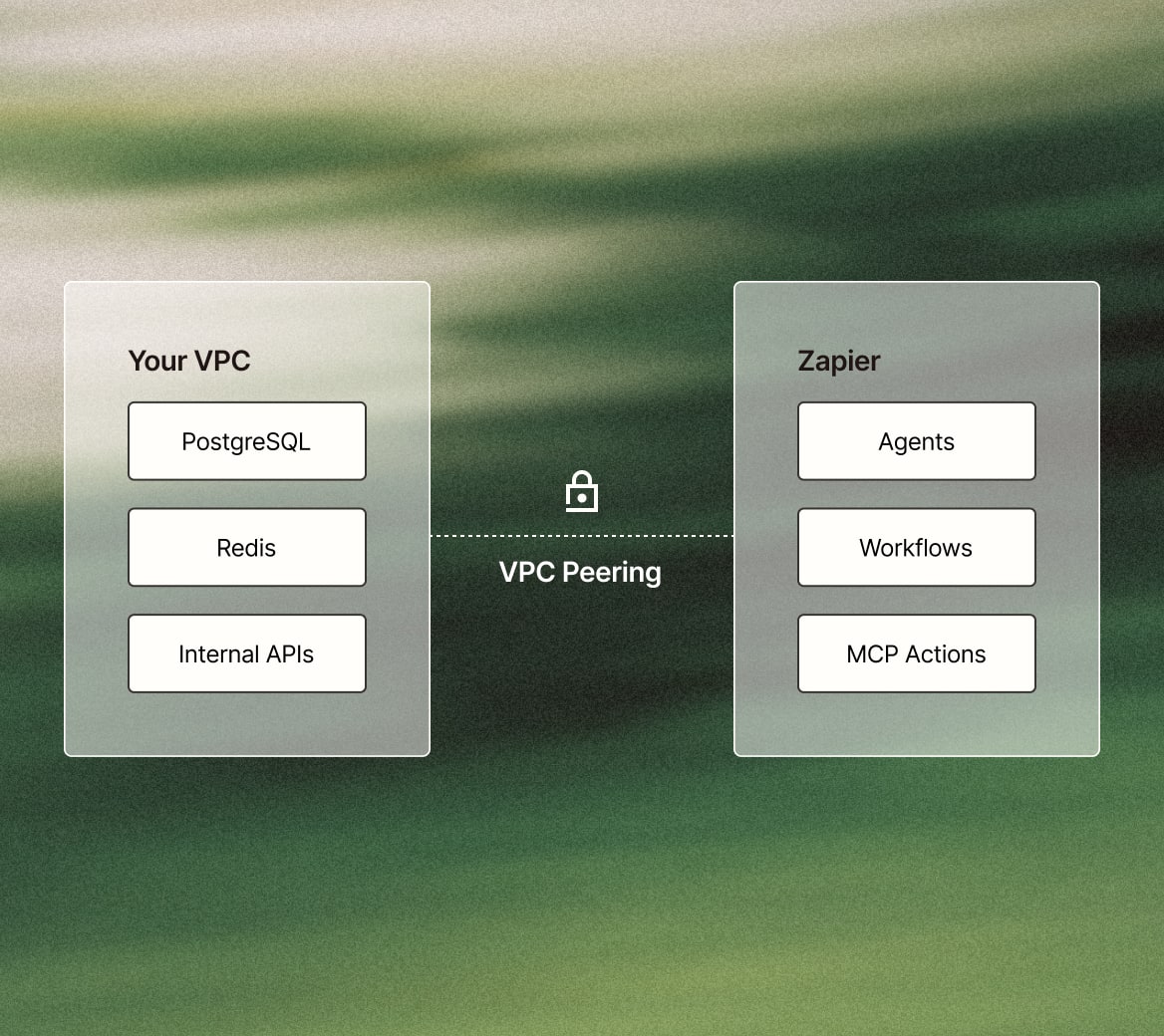
Secure deployment options
Complete audit trail
A foundation built on
data security




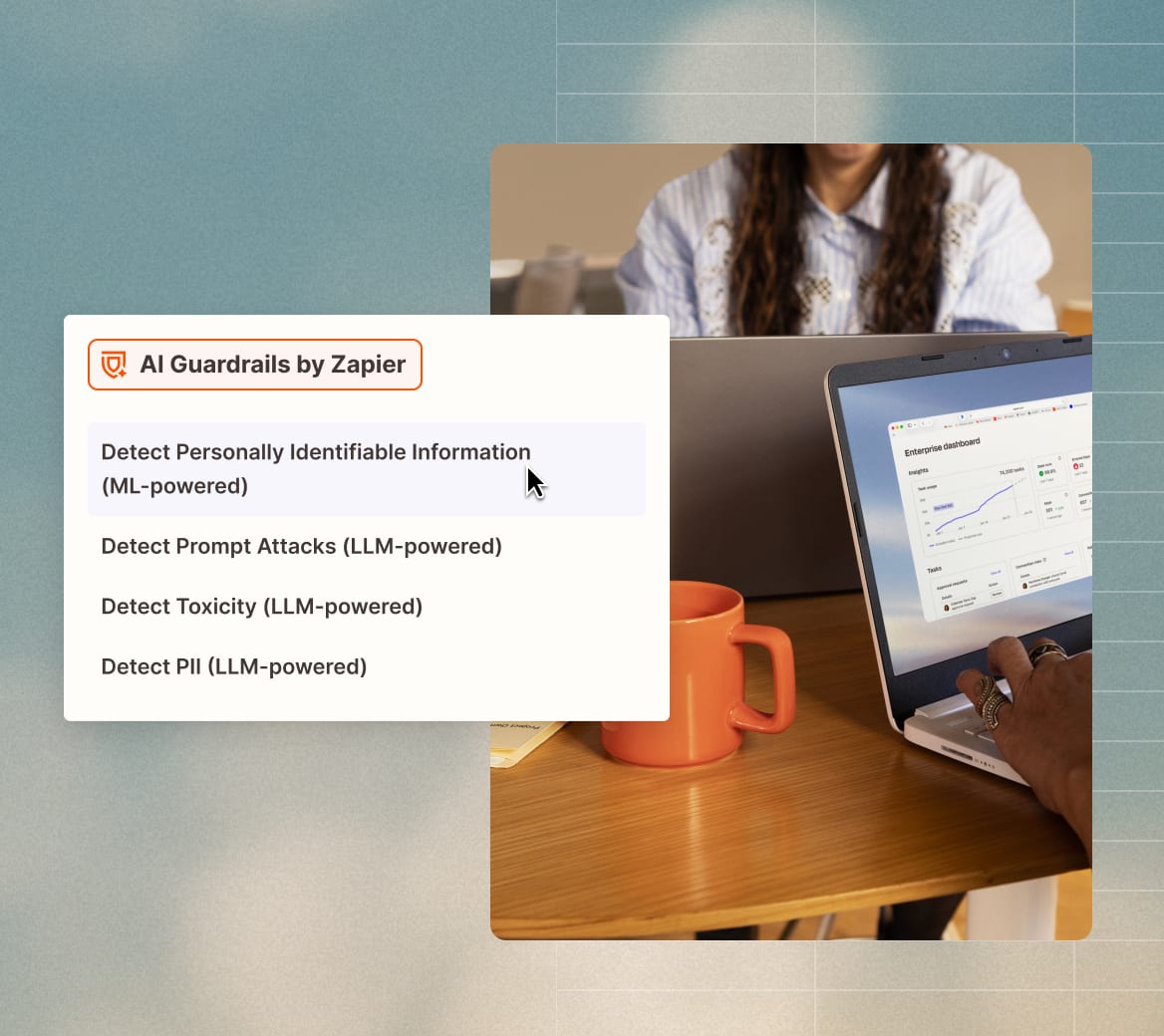
AI Security
Zapier ensures AI-driven automation is secure, transparent, and compliant, giving users full control over data and app interactions.
Features
- Enterprise plan governance
- Turn off AI apps entirely or limit to the ones you want to use
- Model training opt-out
- Automatic opt-out for Enterprise customers, and easy opt-out for all other customers
Reliability
With automated high availability, fault tolerance, and built-in redundancy, Zapier keeps mission-critical workflows running smoothly.
Features
- Outage detection
- Keep your data safe when partners experience downtime
- Intelligent throttling
- Never lose data, even during peak traffic
- API change management
- Zero workflow disruptions when partner APIs evolve
- Data checkpoints
- Complete confidence your workflows will always finish
- Horizontal scalability
- Handle fluctuating workflow volume without performance degradation
Data security and privacy
Zapier protects sensitive data with enterprise-grade encryption, strict access controls, and compliance with GDPR, SOC 2 (Type II), and CCPA.
Features
- AWS cloud security
- Enterprise-grade infrastructure trusted by industry leaders
- Bug bounty program
- Continuous security improvement through ethical hacker insights
- Annual third-party penetration tests
- Independent verification of our robust defenses
- Security logging and monitoring
- Real-time threat detection for immediate response
- Custom data retention for Zaps
- Control exactly how long your sensitive data remains
- Encryption in transit to all Zapier products
- Your data is protected en route
- Encryption at rest (AES-256) to ensure safe data storage
- Enterprise-grade security for your stored information
Governance and observability
Zapier provides real-time audit logs and granular permissions for complete security oversight and control.
Features
- SSO (SAML)
- Seamless secure access with your existing identity provider
- IP allowlist
- Restrict access to trusted networks only
- Domain capture
- Complete visibility and control of your organization's Zapier usage
- 2FA
- Add an essential second layer of protection to prevent unauthorized access
- Analytics and Zap runs API
- Data-driven insights to optimize your automation security
- Application controls
- Granular permissions to enforce your security policies
- SCIM
- Automate user provisioning for efficient access management
- Audit logs
- Complete visibility into user actions for compliance and security tracking
- Shared app connections
- Centralized credential management for enhanced security
Security is just one layer
- App access controls — allowlist and blocklist
- Action restrictions — endpoint-level control
- Managed connections — company-owned credentials
- Domain restrictions — block personal accounts
- AI model policies — BYOM (Bring Your Own Model) configuration
- Workspace management — federated governance
FAQs
What security measures does Zapier implement to protect user data?
Is Zapier compliant with SOC 2 and SOC 3 standards?
How does Zapier handle data privacy in AI functionalities?
Does Zapier use customer data to train AI models?
What cloud service provider does Zapier utilize?
Does Zapier offer two-factor authentication (2FA)?
How can I review Zapier's security practices?
What is Zapier's approach to vulnerability management?
Where can I find Zapier’s SOC 2 and SOC 3 report?
How does Zapier monitor and log user activities?
Ready to explore Zapier’s security in detail?
Talk to our team about your security requirements. We'll share documentation, answer technical questions, and walk you through our governance capabilities.